Handbrake is a hugely popular video transcoding app for the Mac, but that popularity was dented when the creators of the open source app announced that it had been the victim of a Trojan attack. The result was that for a few days, anyone who downloaded Handbrake may have also downloaded the Trojan to their Mac.
How to tell if you downloaded the Apple Handbrake virus
The Handbrake virus isn’t a virus at all because it doesn’t self-replicate. It is a Trojan called Proton that was bundled with copies of Handbrake downloaded from the official Handbrake site during a five-day period. According to a statement on the website, anyone who downloaded the app during that period had a 50% chance of also downloading the Trojan. The period in question was between May 2, 2017 (14:30 UTC) and May 6, 2017 (11:00 UTC). If you didn’t download Handbrake during that period, you wouldn’t have downloaded the Trojan. The reason that only 50% of downloads were affected was that the infection only affected one mirror site for Handbrake downloads.
Obviously, it’s difficult to remember such a specific time period such a long time ago. Fortunately, there is another way to check if you still have the installer in your Downloads folder or elsewhere on your Mac. Again, given that we’re talking about a period some time ago, this is unlikely, but perhaps there’s a Mac you don’t use very often or one you haven’t used for some time. If so, here’s what to do:
- Go to Applications > Utilities and double-click Terminal to launch it.
- Type
shasum -a 1 - Next, type space, followed by the path to the file. The easiest way to do that is to navigate to the file in the Finder and drag it on the Terminal window. Alternatively, if the file is in your Downloads folder, the path will look like this “/Users/username/Downloads/HandBrake-1.0.7.dmg”, where “username” is your account username.
- Hit Return. You’ll now see a string of alphanumeric characters after an “=“ sign. Compare that string with this: “0935a43ca90c6c419a49e4f8f1d75e68cd70b274”
- If that doesn’t match, go back to Step 2, replace the “1” with “256” and in Step 4, compare the result with this: “013623e5e50449bbdf6943549d8224a122aa6c42bd3300a1bd2b743b01ae6793”
- If that doesn’t match, you haven’t downloaded the Trojan. If one of the strings above does match what you see in Terminal, you’ve downloaded a copy of Handbrake that was infected. Read on to find out how to get rid of it.
How to remove Apple Handbrake virus from your Mac manually
- Go back to Terminal and type
launchctl unload ~/Library/LaunchAgents/fr.handbrake.activity_agent.plist - Hit Return and then type
rm -rf ~/Library/RenderFiles/activity_agent.app - Hit Return.
- Go to ~/Library/VideoFrameworks/ and look for “proton.zip”. If it’s there, drag it to the Trash.
- Go to your Applications folder and drag the Handbrake application to the Trash.
- Empty the Trash.
How to remove Apple Handbrake virus the easy way
If all that seems complicated or if you are wary of using Terminal, there is an easier way. CleanMyMac has a built-in malware detection and removal tool, and it’s simple to use. Here’s how:
- Download and install CleanMyMac.
- Launch CleanMyMac from your Applications folder.
- Click on the Malware Removal utility in the left sidebar and press the Scan button.
- If the scan finds anything, press Remove to get rid of it.
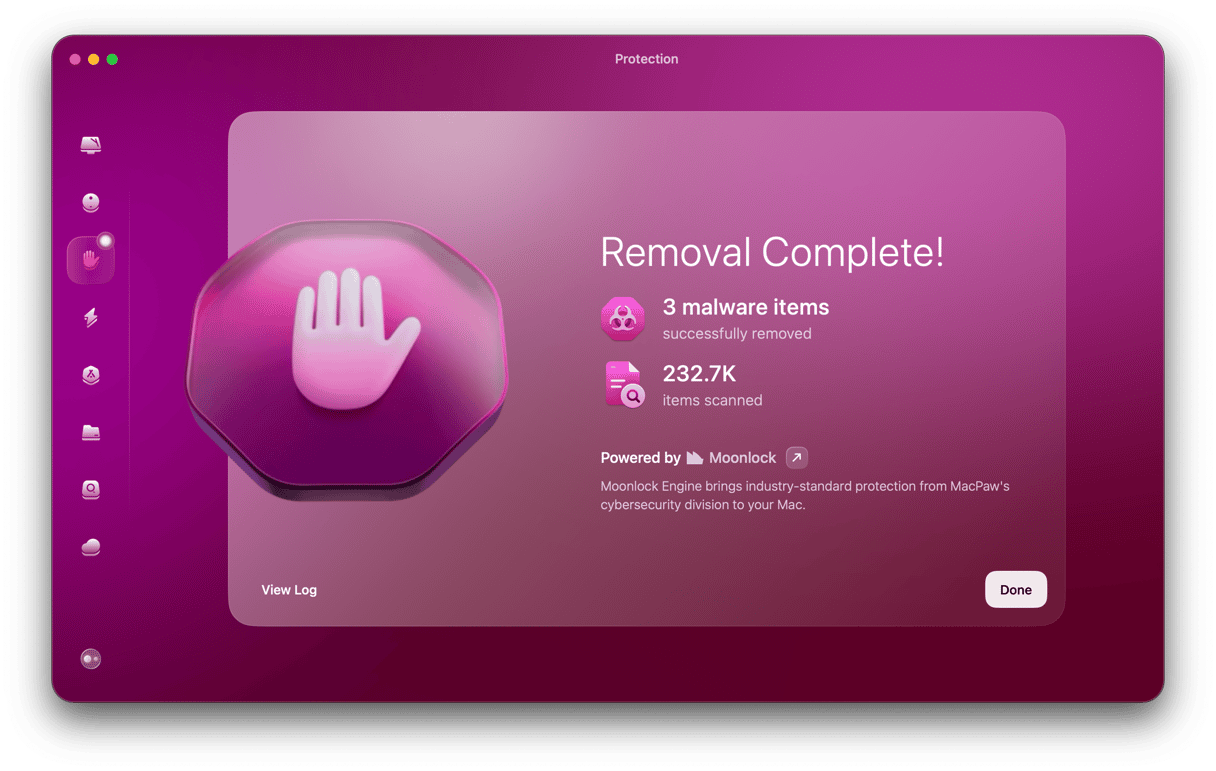
CleanMyMac removes all traces of malware it finds. It maintains an up-to-date database of known malware and compares what it finds on your Mac with that database. By scanning your Mac regularly, you’ll be secure in the knowledge that your Mac is free from malware.
The Handbrake Trojan targets passwords stored in the keychain and in browser-based password managers, such as the one in Safari. So if you have downloaded it, you should change all the passwords that are stored either in a keychain or a browser. Just removing them from Keychain Access or the browser’s stored passwords isn’t enough. You’ll have to log into each account and change the password.
The Proton Trojan that hit copies of Handbrake was a malicious attack aimed at gaining admin privileges on Macs and using those to target passwords and other details stored in Keychain Access and in the password storage in web browsers like Safari. It was bundled with Handbrake on one download mirror for several days. However, removing it is straightforward, albeit a fairly lengthy process involving Terminal commands.
If you prefer not to use Terminal or just want an easy and quick way of removing the Trojan, you can use the Malware Removal tool in CleanMyMac, which can identify and remove it in a couple of clicks.