Have you ever let an IT professional take control of your computer to help you with a problem? A lot of corporations will do this so their IT teams can remotely install apps or help you regardless of where you are. It’s an incredibly useful tool – when it’s in the right hands. But sometimes, remote access tools are used by cyber criminals, and one such tool is Nanocore. Keep on reading to learn what it is and how to remove it from Mac.
| Name | Nanocore |
| Category | Remote access tool |
| Symptoms | It’s designed to be undetected, so it has no identifiable symptoms |
| Infection method | Infected emails attachments, redirected ads, and bundled software |
System damage | Compromised data and banking information, and system control |
| Removal | Manual removal or removal with CleanMyMac |
What is Nanocore?
Nanocore is commonly called a remote access tool, or RAT, designed to take control of your Mac secretly. Once it does that, it has complete access to your hard drive and can allow other malicious software to run amok. Not only can Nanocore open a backdoor for other software, but it can also take control of things like your microphone or camera — going a step beyond just stealing your information but also invading your privacy.
How did Nanocore get installed?
The most popular way Nanocore spreads from computer to computer is through infected email attachments. This is why it’s so important that you only open attachments from people you know and trust. Otherwise, you could be opening up your computer to a whole world of frustration if you’re not careful.
Other popular methods for installing Nanocore are using browser redirects and social engineering. For example, it will redirect you to ads that appear to be antivirus or app updaters when, in reality, it’s Nanocore tricking you into installing a version of it on your Mac.
How to remove Nanocore manually
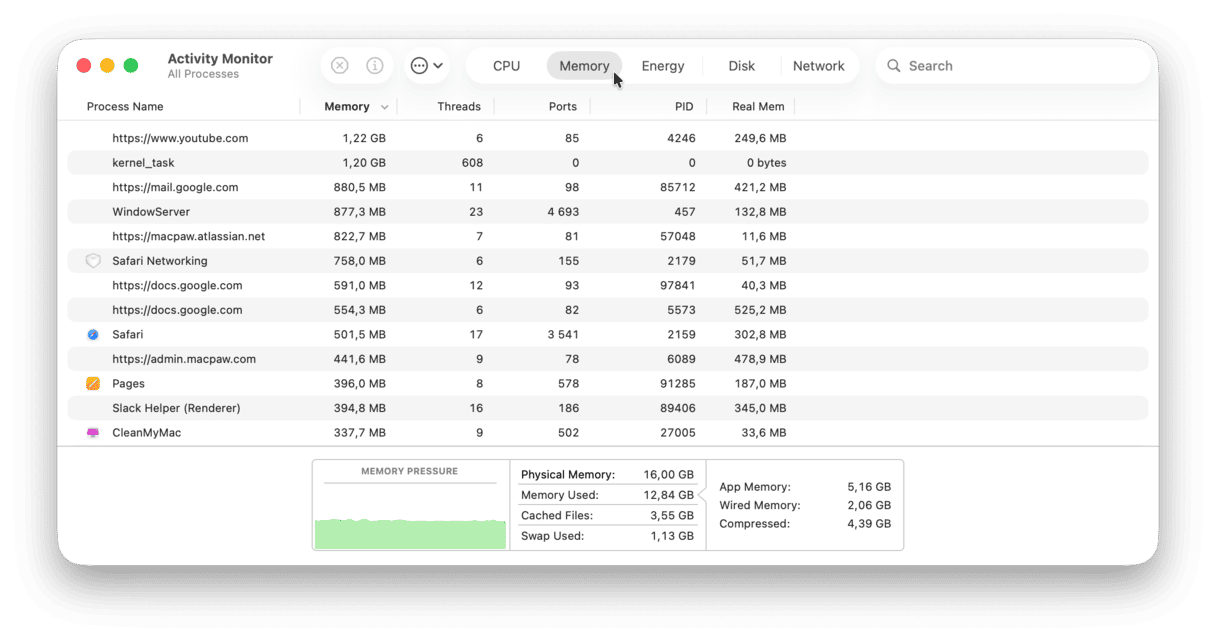
Since Nanocore is virtually undetectable, getting rid of it is going to require just a little bit of work. The first thing you’ll need to do is force quit out of any apps that Nanocore is posing as.
Here’s how you can do that:
- In a new Finder window, click Go > Applications > Utilities.
- Look for a process that looks suspicious and is using a ton of processing resources.
- Select that process and click the Stop icon at the top.
- Confirm to Force Quit the apps.
After you force quit the app(s), you’ll want to remove any files that are buried deep in the system library by following these steps:
- Back in Finder, click Go > Connect to Server.
- Type
Library/LaunchAgentsin the dialogue box. - Click Go.
- Again, see if you have any suspicious files in there, and then just delete them.
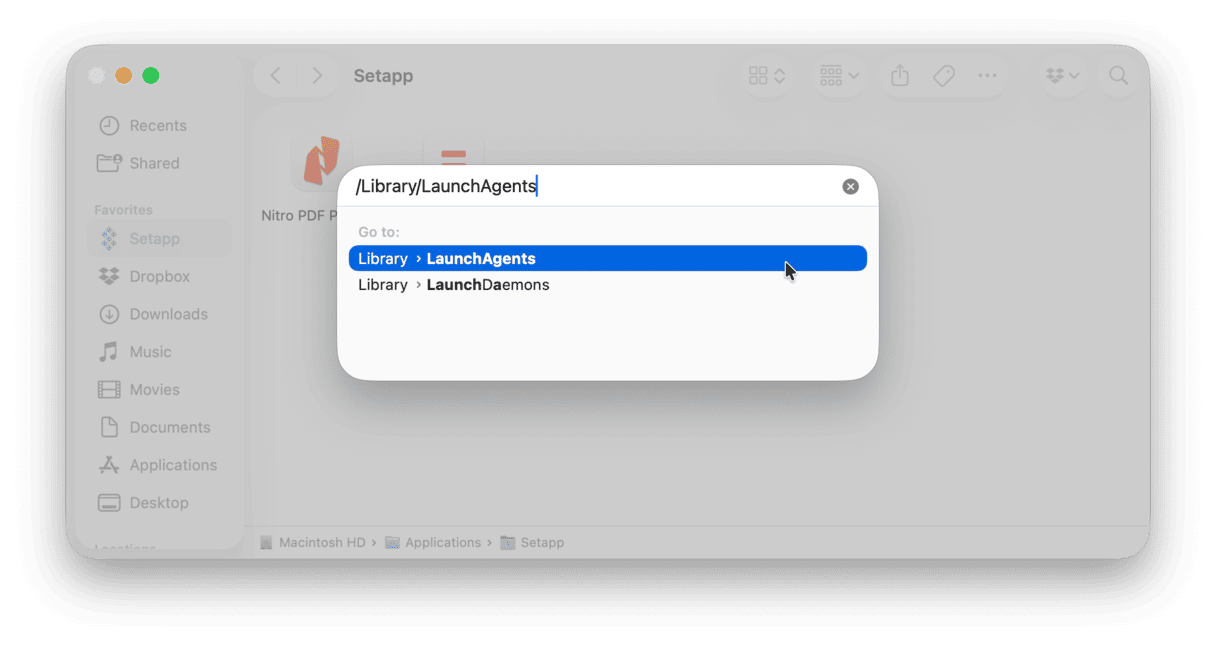
You’ll need to repeat these steps, but in step 6, you’ll want to navigate to different folders. Here’s a list of folders that you’ll want to go through both in the system library and user library:
Library/LaunchAgents~/Library/Application Support~/Library/LaunchAgents/Library/LaunchDaemons
Once you clear out all of those supporting files, you should restart your whole computer. It gives your Mac the chance to start fresh and reload the software you have installed.
Get rid of other malware installed on your Mac
Since you can’t tell when you have Nanocore installed, there’s no telling how much malware it might have installed, too. So it’s a good thing to frequently scan your computer for any dubious software lingering on your hard drive.
Fortunately, the app CleanMyMac is a great tool. It will scan your hard drive and automatically get rid of any of the malicious software it finds. In fact, here’s how easy it is to use CleanMyMac to get rid of malware:
- Open CleanMyMac (get your free trial here)
- In the sidebar, click Protection and run a scan.
- If any malware has been detected, click Remove.
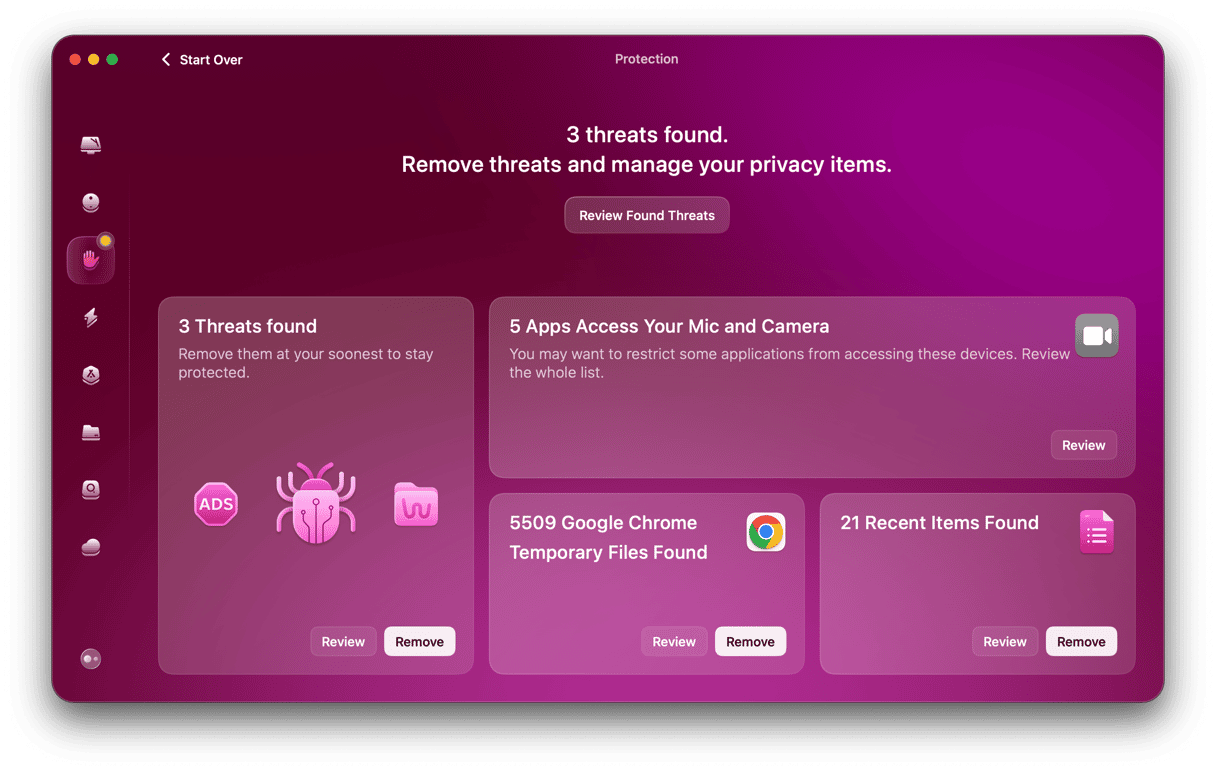
That’s really all there is to it. Since that was so simple, check out other issues CleanMyMac may have found. Review privacy items to clear up recent items lists and browser data as well as revoke excessive app permissions. This way, you can elevate your privacy to a whole new level with just a few clicks.
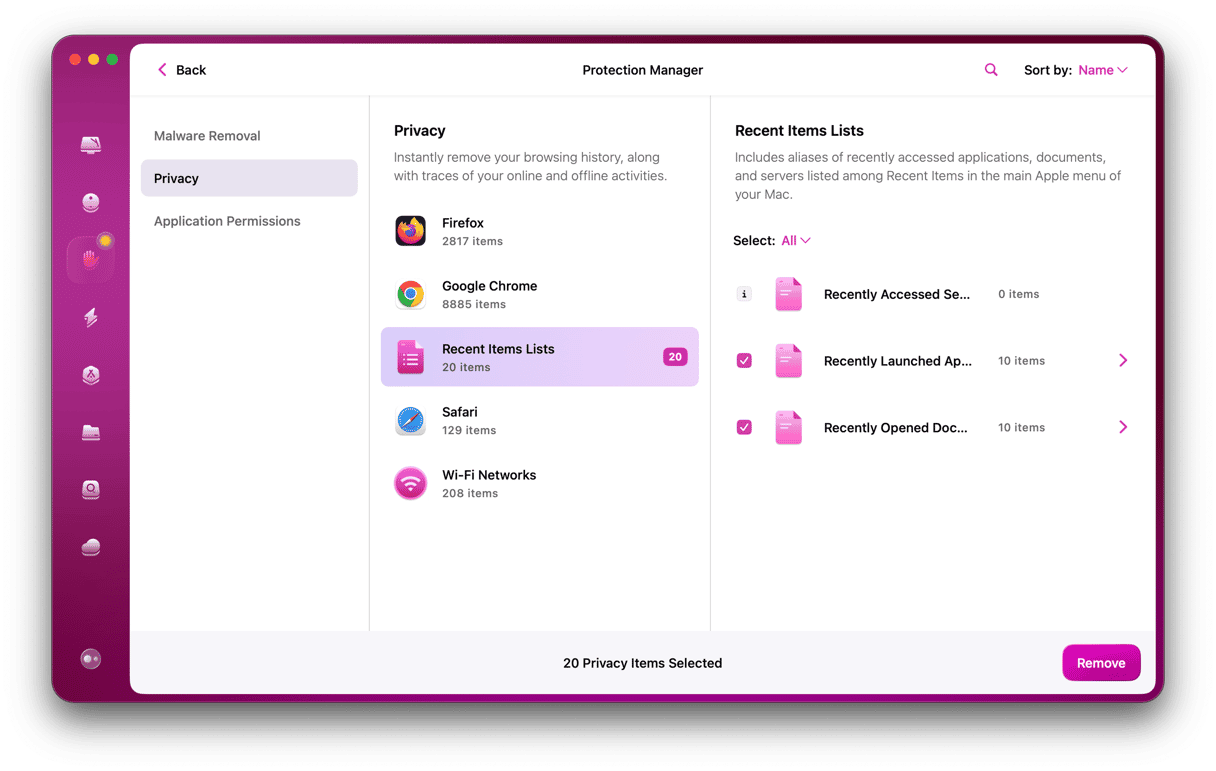
As you will see, the results of the Protection feature scan with CleanMyMac will show you all the vulnerabilities you have on your MacBook. So it’s pretty straightforward and helpful to support you in staying secure.
Don’t let yourself lose control over your computer to a RAT like Nanocore. It sneaks onto your computer and steals your private data without you even realizing it. Even if you already had Nanocore or something equivalent installed, hopefully, you found this to be helpful. And are more confident in when to trust remote-access tools and when to be a little more cautious.