As the scope of internet usage expands, tracking user information is becoming more and more lucrative to a variety of entities. In many cases, these tracking activities are actually legal, such as in the case of product targeting. Product targeting is the practice of advertisers gaining information from a person's search history in order to tailor the advertisements that the user sees to be more appealing to them.
According to a study by InMoment, 75% of customers find personalized ads "somewhat creepy."
Worse still, there are also many illegal ways in which this is done maliciously. Tracking of internet history may be concerning to many users, not only as it pertains to hacking and theft of information, but also to technically legal tactics that are annoying or invasive.
How to protect your identity online
1. Clear cookies and other browser data
There are tools to remove the traces of your recent online activity. Some of them are even freemium, meaning some part of their functionality is free.
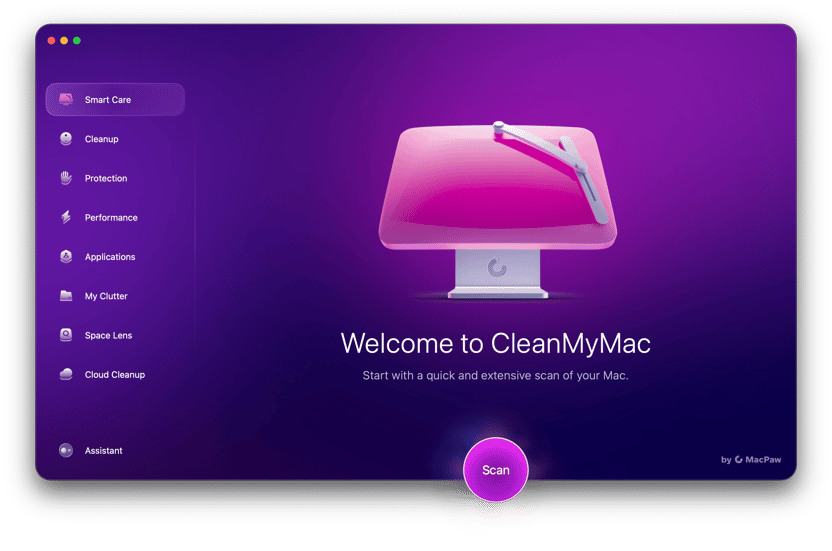
One such digital trace remover is CleanMyMac (if you're on the Mac).
It will delete your cookies in Safari and other browsers. Here's how:
- Open CleanMyMac and click Protection > Scan > Manage Privacy Items.
- In the Privacy tab, select the browser and the data you want to get rid of and hit Remove.
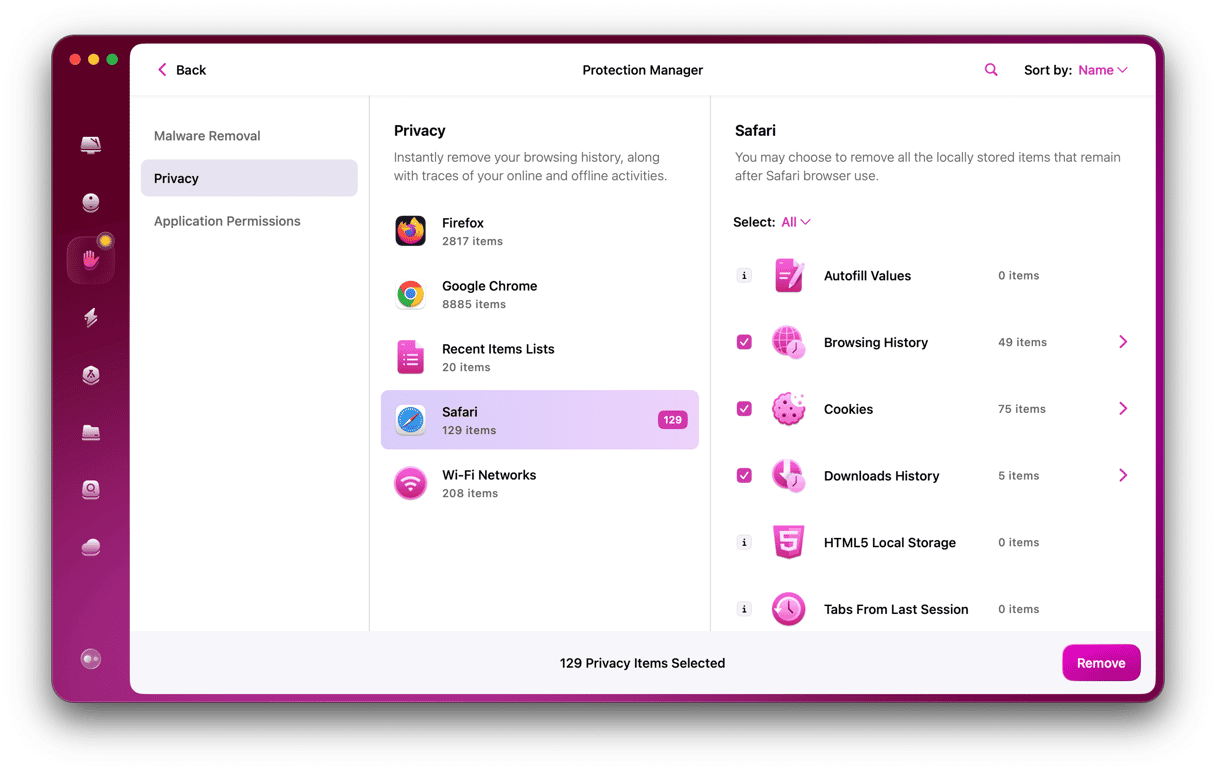
You can test the app for 7 days at no cost — get your free trial here. This program is notarized by Apple, so no red flags here.
2. Use stronger passwords
Passwords and usernames are a decent first layer of defense, but they alone certainly will not stop your information from being documented. In fact, despite the reputation of increased security some computers (such as Mac products) enjoy, no computer is completely safe or anonymous. However, it is possible to take simple measures to bolster your defenses against malicious or annoying lurkers, such as through the use of third-party software, and with mindful computer usage.
3. Use anonymous browsers
A simple step an internet user can take to protect their privacy is choosing their browser carefully. Not all browsers are created equal in terms of privacy protection policies. For example, Safari blocks websites from leaving data in the user's cache, which is one of the most common ways that advertisers track users and their information.
There are also plug-ins available that allow users to remain anonymous on the internet, and search engines like DuckDuckGo that prioritize the protection of user information over the personalization of search results.
4. Don’t give away personal information
While the thought of advertisers tracking your search history may be uncomfortable, there are also more serious threats on the internet, and the first step to avoiding them is to avoid giving out your personal information. This may seem like obvious advice, but online scams such as phishing are becoming increasingly crafty.
Furthermore, malicious users don't necessarily need your Social Security number to cause trouble. Information easily found on a social media page could be enough to cause damage. It may be advisable to avoid posting personal phone numbers, email addresses, or home addresses on social platforms, unless you are listing fake details. This information can be used for many nefarious purposes, such as phishing, tracking your location, or acquiring access to online accounts.
5. Increase privacy settings
Storage and the tracking of information are actually often used to improve user experience, such as by documenting frequently visited websites. For this reason, much of your information is stored automatically by your browser. As a result, visiting an unsafe website may cause your personal data to be exposed.
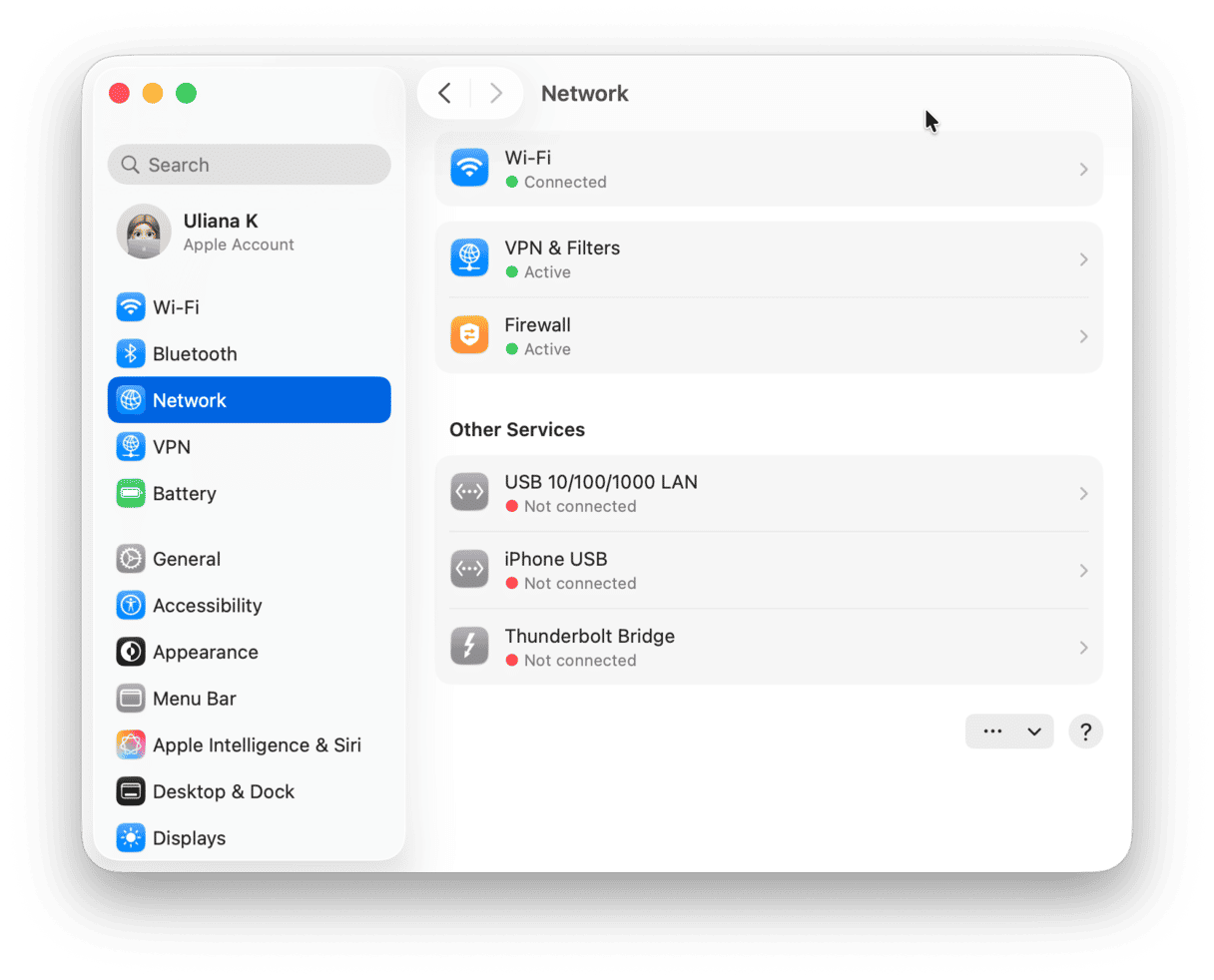
The first step in that direction is to enable the Firewall in Apple menu > System Settings > Network > Firewall.
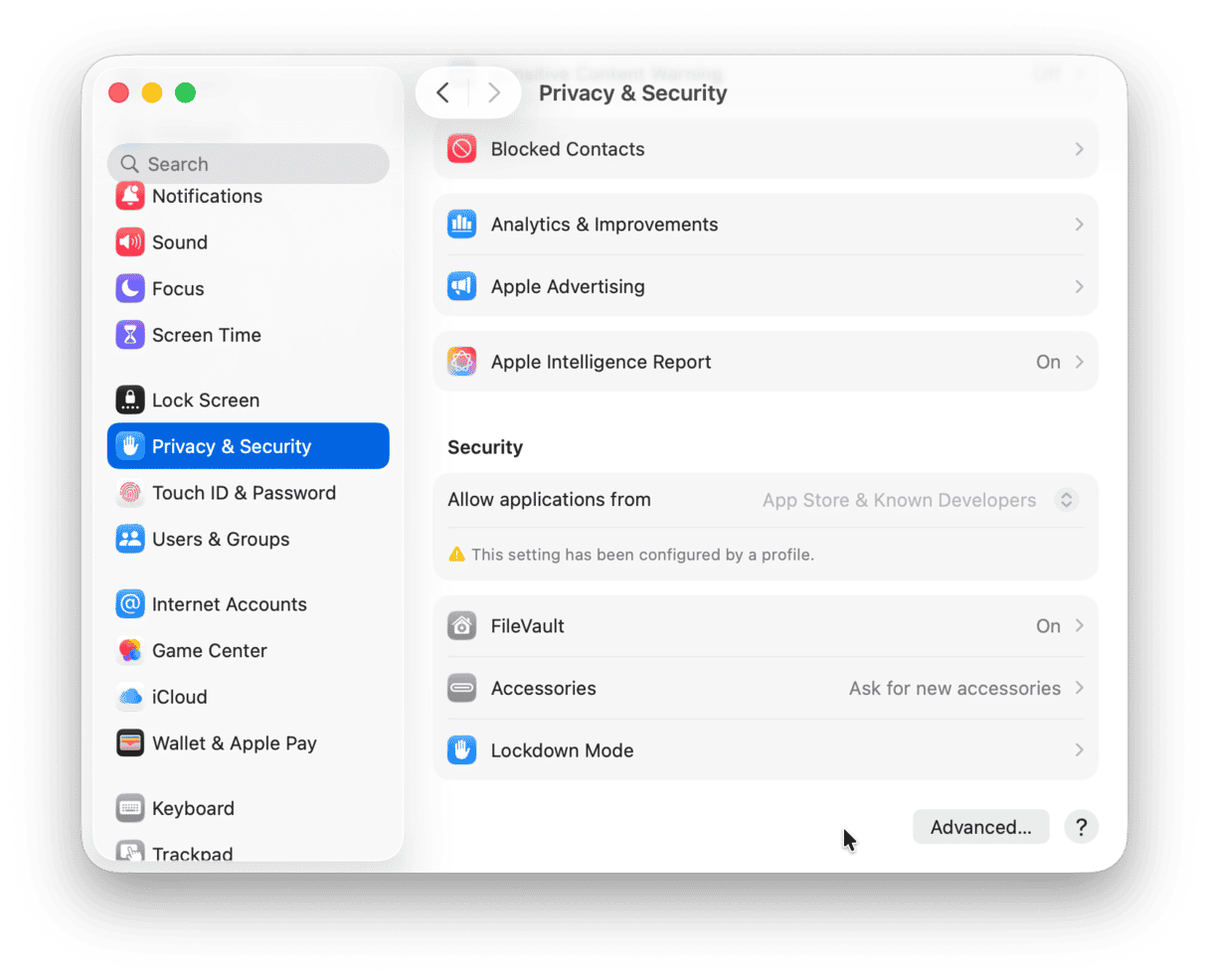
In order to avoid this risk, you could use a third-party platform that utilizes substitute personal information, or you can adjust the privacy settings on your computer. On a Mac, privacy settings can be adjusted by selecting “Privacy & Security” in System Settings. By tweaking privacy settings, a user can alter everything from location services to app permissions.
6. Watch out for spam
Oftentimes, when you visit a website, there’s a gateway that requests you provide your email. Sometimes you are further given the option to not receive notifications from the site, but these cases are few and far between. This often results in a deluge of annoying spam emails or even more malicious outreach, such as phishing and viruses. Beyond declining and blocking emails, the best way to prevent harm from these schemes is to run regular antivirus diagnostics and periodically clean up your drive.
7. Use two-factor authentication
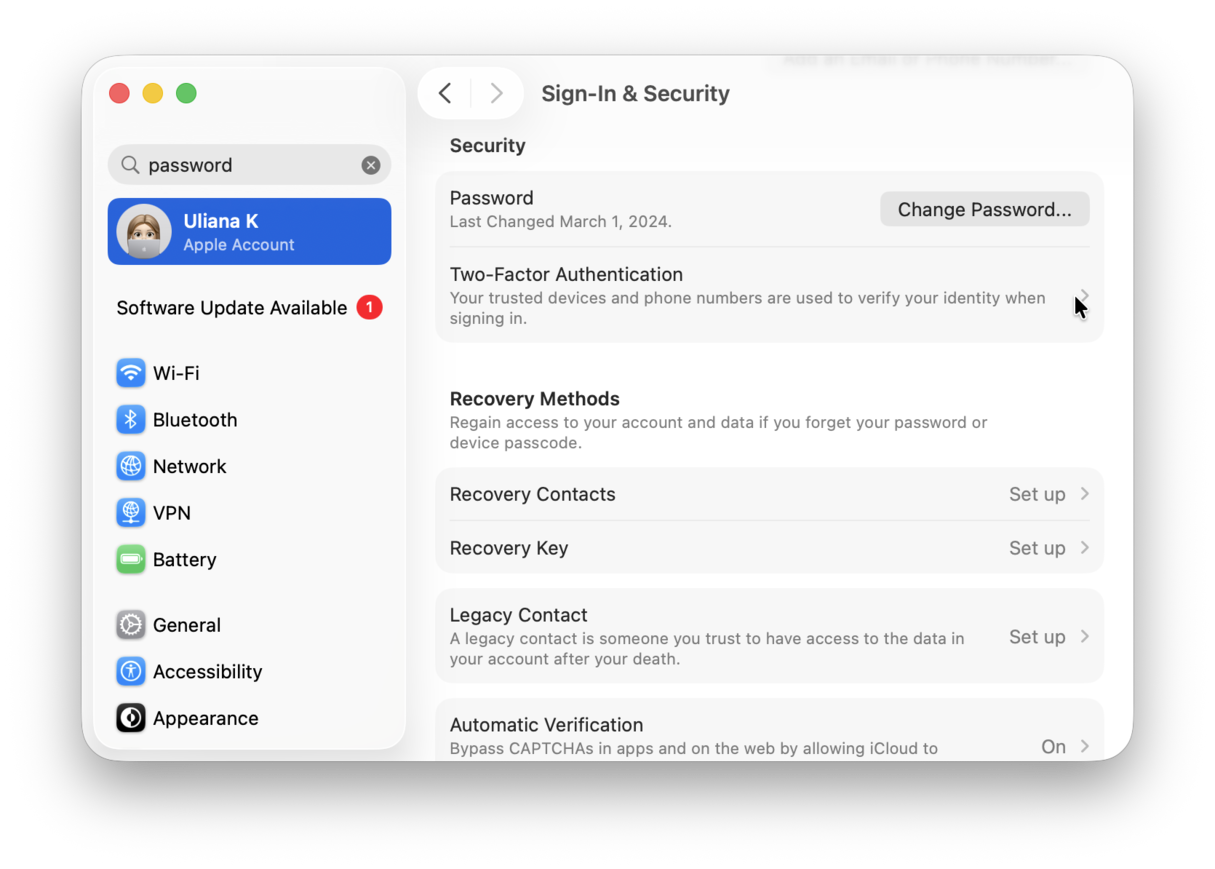
As the term implies, two-factor authentication is a process by which users confirm their access on two different levels. This is a great way to circumvent many forms of malicious documentation of your personal information. For example, password access would account for one factor of authentication, while something like a flash drive or a fingerprint may account for the second. This gives any would-be hackers more hurdles to cross. Mac devices, for instance, give users the option of two-factor authentication in the form of a password and a verification code. This option can be accessed in Sign-In & Security under System Settings > Apple Account.
More identity protection tips:
- Don’t give away your real email to access a public Wi-Fi network
- Visit the Privacy settings for any new service you’re about to subscribe.
- Cover your webcam and microphone with tape (but remove them when closing the lid)
- Stay away from Facebook polls that involve face recognition
When subscribing to a new website, use the name of that company as your family name. For example: Jack FreeTemplatesCom. This way, if the company ever leaks your data, you will know the source of the leak.
8. Invest in a VPN
Another hurdle for potential hackers is the use of a VPN(a virtual private network). MacPaw's own ClearVPN creates a private network within a public network. These networks are often encrypted, which adds an element of security to the space. ClearVPN also hides true IP addresses within the network and replaces them with a dummy IP address. This makes it much more difficult for the users’ activity to be tracked. ClearVPN is the first effortless VPN solution for a personalized and secure online experience.
9. Secure Wi-Fi Routers
It is also possible to secure your router itself. To start with, it is important to follow instructions for initial setup carefully and to choose a password that will not easily be guessed. However, there are also more sophisticated options for router security:
- Encryption: Common types of encryption for routers include WEP (Wired Equivalent Privacy), WPA (Wi-Fi Protected Access), and WPA2 (Wi-Fi Protected Access 2).
- Firmware: Your router’s firmware should regularly be updated.
- Firewall: A firewall can filter out potentially harmful or otherwise undesirable websites.
However, the traditional router is not the only option for internet users. For example, many Mac users employ Time Machine backup system software in conjunction with their router hardware for the sake of additional security. Although Wi-Fi passwords provide a modicum of security, there are many ways to bolster the security of your router.
A combination of simple precautions and the utilization of security tools can make an internet user’s experience both safer and more enjoyable. By running CleanMyMac and performing regular security sweeps, as well as following basic best practices, it is possible to secure your computer and protect your identity online.