Smartphones make our lives easier. We share our life updates on Instagram. We navigate the city via Maps every day on the commute. Apple or Google Pay will help us go cashless. Smartphones are present in all areas of our mundane life. So much, that we entrust them with all our secrets, bank accounts, intimate photos, and videos. But you may ask, what if my device gets hacked? How to protect your phone from being hacked? Leaks of private photos of celebrities prove — hackers can get into your smartphone. Including the cameras and microphone. Hackers will not only spy on you, but they will gain access to all financial data like bank accounts, all your files, photos, and videos. Even geolocation can be recorded. That’s why we’ve prepared cell phone protection tips to help you secure your device from hacking.
How to protect your phone from hackers?
Enable Two-Factor Authentication
Hackers can crack down your password to log in to your account. But not with the Two-Factor Authentication. It’s an extra layer of security designed to ensure that you're the only person who can access your account, even if someone knows your password. When you want to sign in on a new device for the first time, you'll need to provide two pieces of information—your password and the six-digit verification code that's automatically sent to your phone number. By entering the code, you're verifying that you trust the new device.
Use Strong Passwords
Don’t use years, pets’ names, or popular words! A strong password is long (more than 7 digits). It includes upper-case letters, lower-case letters, numbers, and special characters. Don’t use one password with all accounts! If a leak happens, the hackers will receive access to all web services you use. If you think you’ve created a strong password — you can test it on this website.
Use apps ONLY from Google Play or App Store
Each new app is reviewed by experts from the app distribution services. Google uses both manual and automated app review systems. It checks the new app for compliance with developer guidelines. The Apple team also downloads new apps and tests them, but even stricter. While Android Apps usually get approved in 2 hours, Apple can torture the newcomers for up to 2 days. Both companies decline if there’s a small suspicion that the app is malware.
Google Play and App Store developer guidelines require in-app privacy. The apps are obliged to ask for permission to use other smartphone features, like a camera, microphone, geolocation, contacts, and others. If they don’t, they get rejected. Be sure not to download any apps outside the trusted platforms.
Always keep your phone up to date
This may be one of the most subtle cell phone protection tips, however, you shouldn't underestimate how crucial it is. Nothing is perfect — iOS and Android have vulnerabilities that hackers use. But Apple and Google try to cover-up security gaps in their operating system as soon as they detect them. They do it by releasing new updates. Make sure to keep your phone updated. It also includes apps you use — they can also have some holes. Their developers do their best to have the products safe for you. Update them too. Here's our complete iOS update guide.
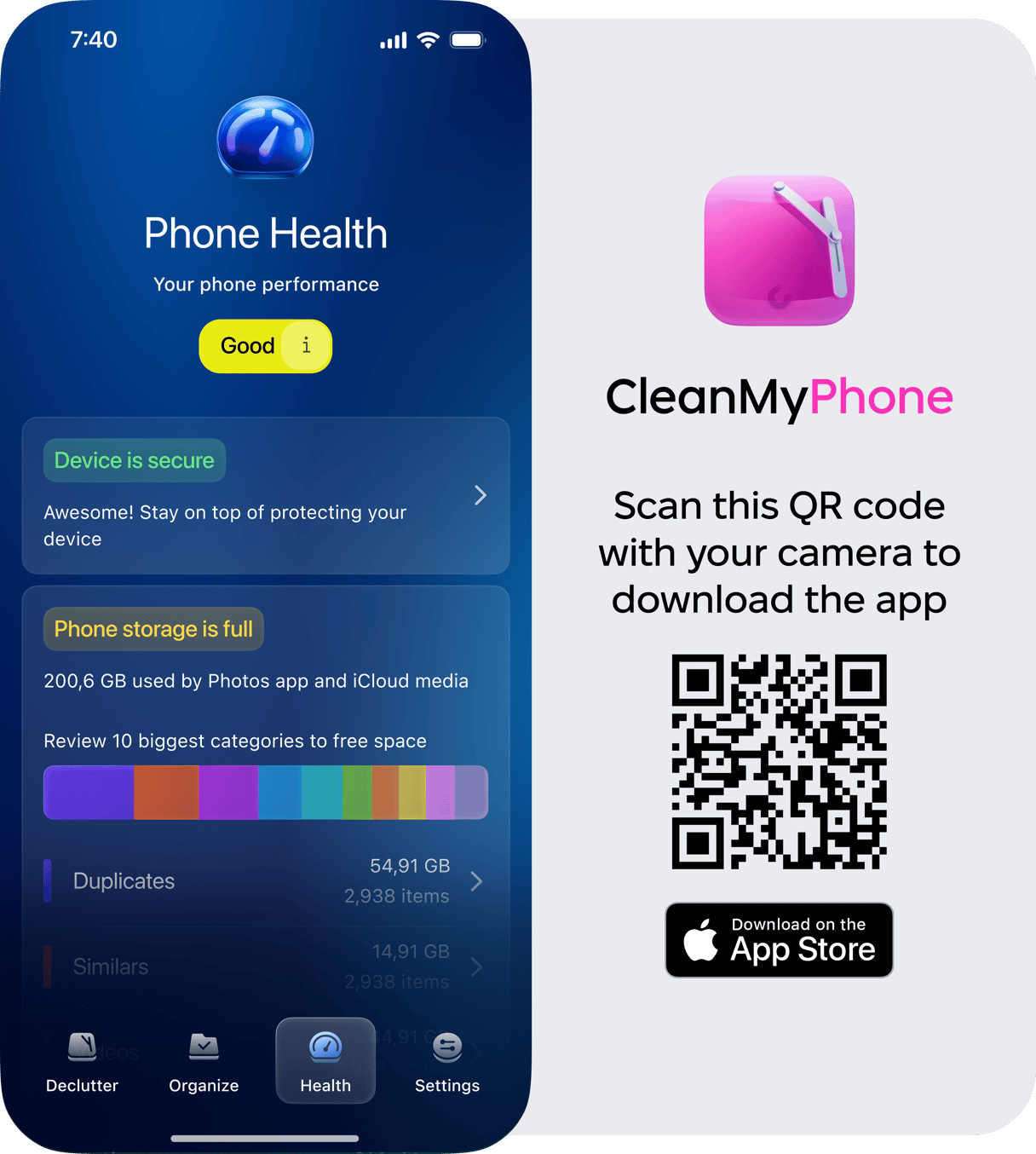
Check if you have enough storage
If your iPhone is lagging, chances are you're low on storage. An app like CleanMy®Phone can help you not only clean up large photo libraries but also provide insights into which photos and videos are taking up the most space.
Check what permissions your apps have in Settings
Yes, it can be surprising that your calculator asks for cellular data and geolocation. Even if it isn’t hacked or spying on you, it can show some annoying ads. Go to your phone settings and check what permissions you granted to your applications. Make sure to allow them ONLY the features they need. Here's how to do that on your iPhone:
- On your iPhone go to Settings > Privacy.
- Choose the feature you want to edit the access to, tap on it.
- Move the toggle to turn off/on the access granted to a particular app.
- Revise all of the features to block apps from compromising your privacy.
_1599139915.png)
Don’t click on random links (even if they are from your friends)
By 2025 we’ve all learned that if a link looks too appealing, it might be a fraud. Hackers have now understood this too. Now their link can lead you to a music video on YouTube. The moment you click on it, the hacker receives your IP address. With it, other attacks become easier to perform.
Use a VPN service
You already know that a VPN is a must-have for free Wi-Fi in cafes and airports. Their connection isn’t encrypted and can be used for a man-in-the-middle attack. Making transactions in such places without proper encryption is dangerous. You can lose money and access to your bank account.
Your home Wi-Fi is also hackable. Yep, even if you have a strong password there. If your home network gets hacked, it’ll put all your smart devices in danger, including your smartphone. Your Internet Service Provider (ISP) can also be hacked. They keep all the data you share across the internet on their servers with no encryption. A hacker just needs to get into that server. There they will receive your IP address, passwords, the time you spend on websites, your habits, your clicks, and even the intimate photos you send to your close ones.
But it won’t happen if you use a VPN. It serves as a midpoint between your smartphone and the internet. VPN also encrypts all the data with high-tier algorithms making sure nobody but you can access your personal messages, photos, emails, and others. Also, a no-log policy is a must-have for a good VPN. It shouldn’t keep your data on its servers.
Using a VPN can be crucial for secure and private online interactions. We take your online safety seriously. That’s why we’ve created ClearVPN — the first effortless VPN for a secure and personalized online experience. ClearVPN is the only VPN you need. Because it clearly understands you.