A typical “Your screen is being observed” message can make anyone feel paranoid. Is it malware or is it a bug? Luckily, in 90% of cases, it simply means that a screen-sharing app hasn’t been turned off. Keep on reading to learn about how to fix it.
What does “your screen is being observed” mean
Before proceeding with the solutions to the Mac screen observed error message, let’s find out what causes it:
- Sharing the screen. The message may pop up when you actually share your Mac’s screen. It can be done either locally or remotely.
- Third-party apps. In this case, the focus is on access to recording the screen you granted to the apps installed on your Mac. You may have missed the point at which it happened or forgotten about that.
- AirPlay. Streaming video and mirroring screen are convenient Mac features. However, they may cause the message, and if it remains unnoticed for some time, it may be alarming once you finally discover it.
- Screen recording. It may be that you are recording the screen, and it will show the same message as in the case of the third-party app observing it.
- Malware. Unfortunately, Macs are susceptible to being infected, and some forms of malware observe your screen to collect your sensitive and private information as well as the details about your activities.
Note that you may see it even if your Mac is offline because a process or a recorder may run in the background even if you locked your Mac or put it to sleep.
How to stop Mac screen from being observed
Now that you know what may cause the message, let’s see what can be done to fix the issue. These are the solutions to all of the reasons outlined above.
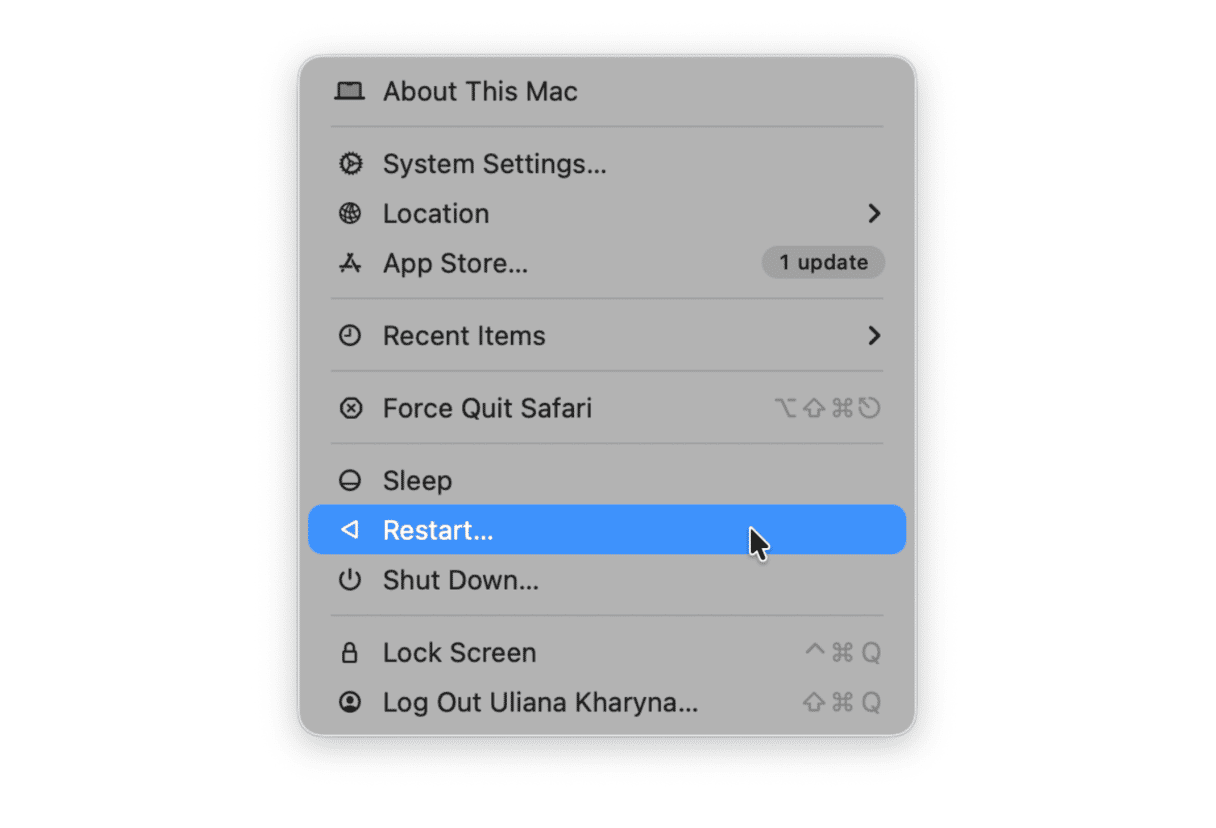
Restart your Mac
Usually, it is the very first thing to do to fix any error message. Sometimes, it works with this one, too. So, go to the main Apple menu and choose Restart.
Check sharing settings
As noted, screen sharing may be either local or remote. However, there is one more thing to mention — it can be either intentional or by mistake. Fixing it, though, is easy and straightforward:
- From the main Apple menu, go to System Settings > General > Sharing.
- Make sure that Screen Sharing is turned off.
- Also, turn off Remote Management.
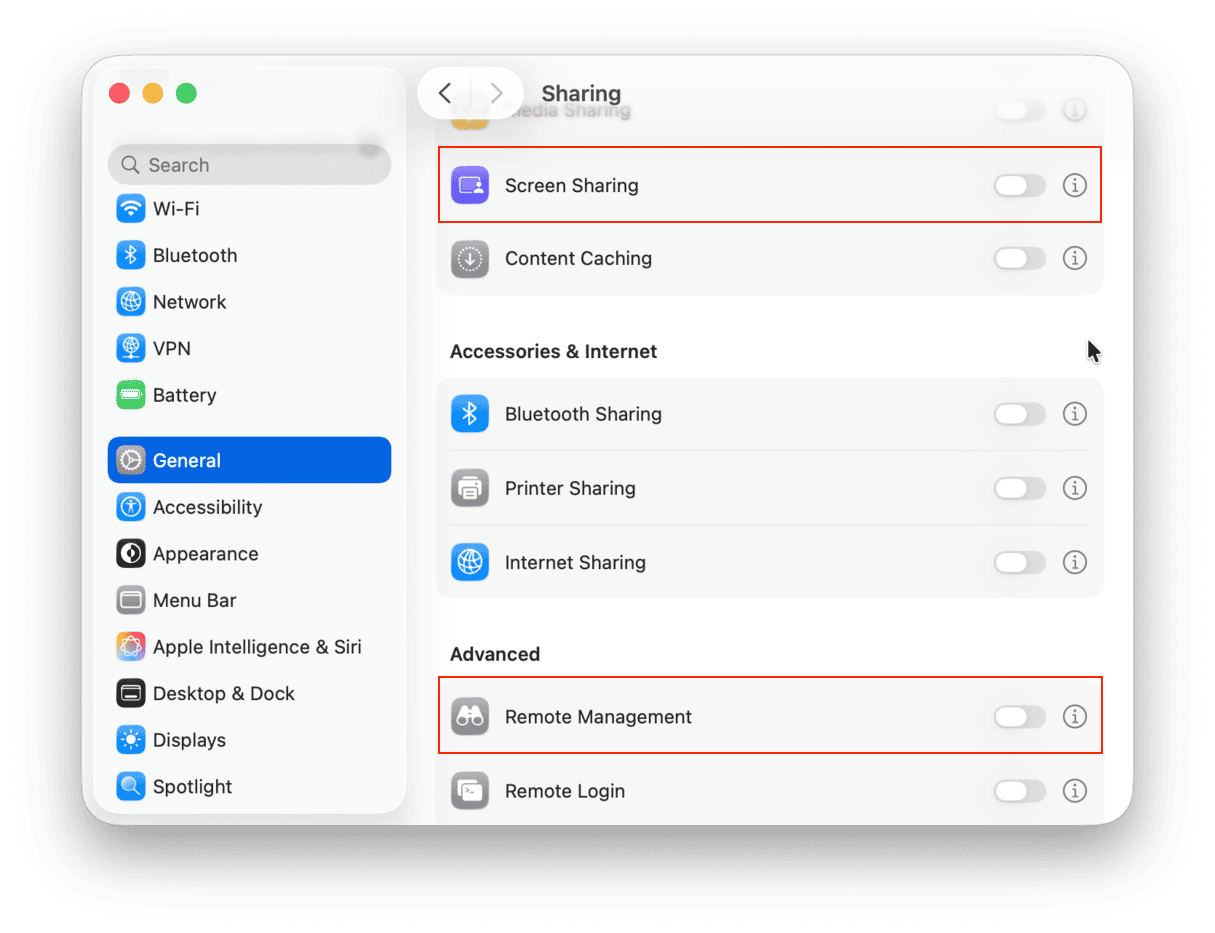
If Remote Login is also enabled, it may mean that your Mac is observed by an employer. If it is not a corporate MacBook, you can disable this option, too. If it is a corporate computer, contact your admin for further instructions.
Hopefully, it should help address the issue; if not, keep on reading.
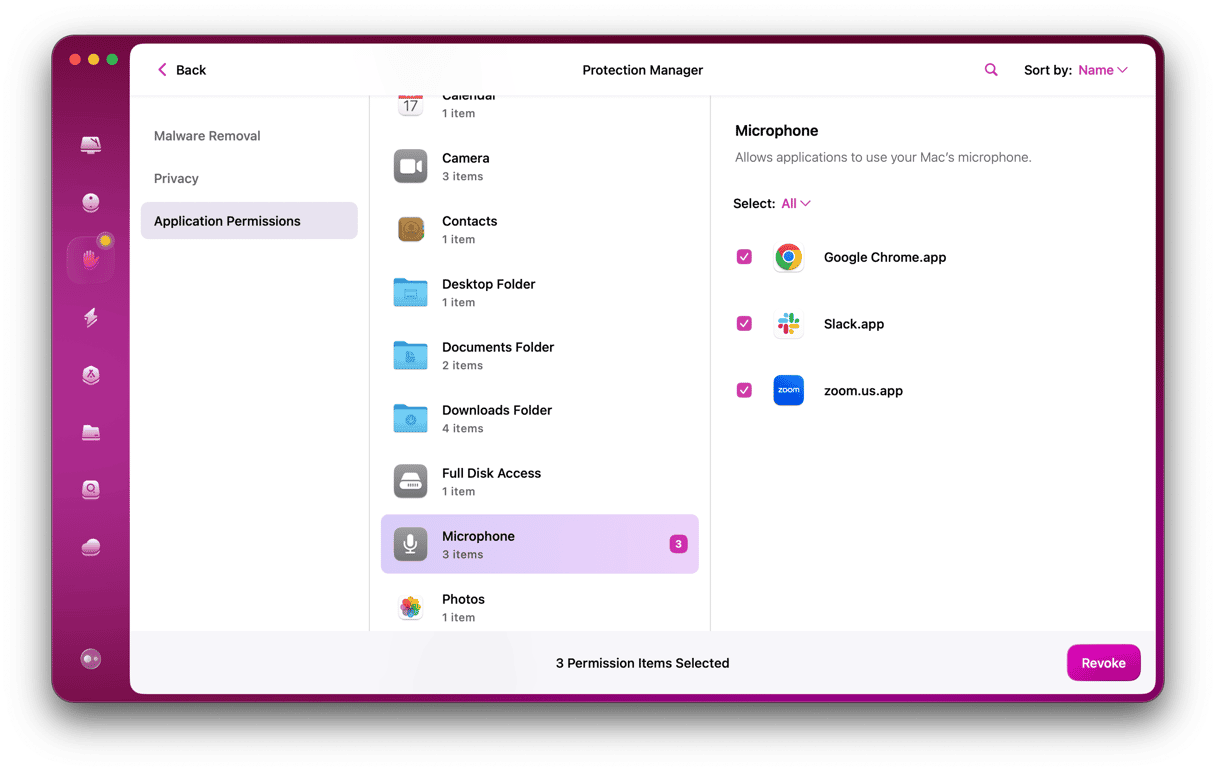
Check what apps have access to your screen
You may see the message telling you about the Mac screen being observed if some apps you’ve installed on your Mac attempt to access the screen. In this case, the issue goes beyond the annoying message; it is more about privacy. It means that reviewing app permissions may not only fix the issue but also give you some peace of mind by protecting your sensitive information from prying eyes.
To check permissions, do the following:
- Go to Apple menu > System Settings > Privacy & Security > Screen & System Audio Recording.
- From here, check the apps on the list and remove anything that you do not want to access your screen by clicking -, and it will be gone.
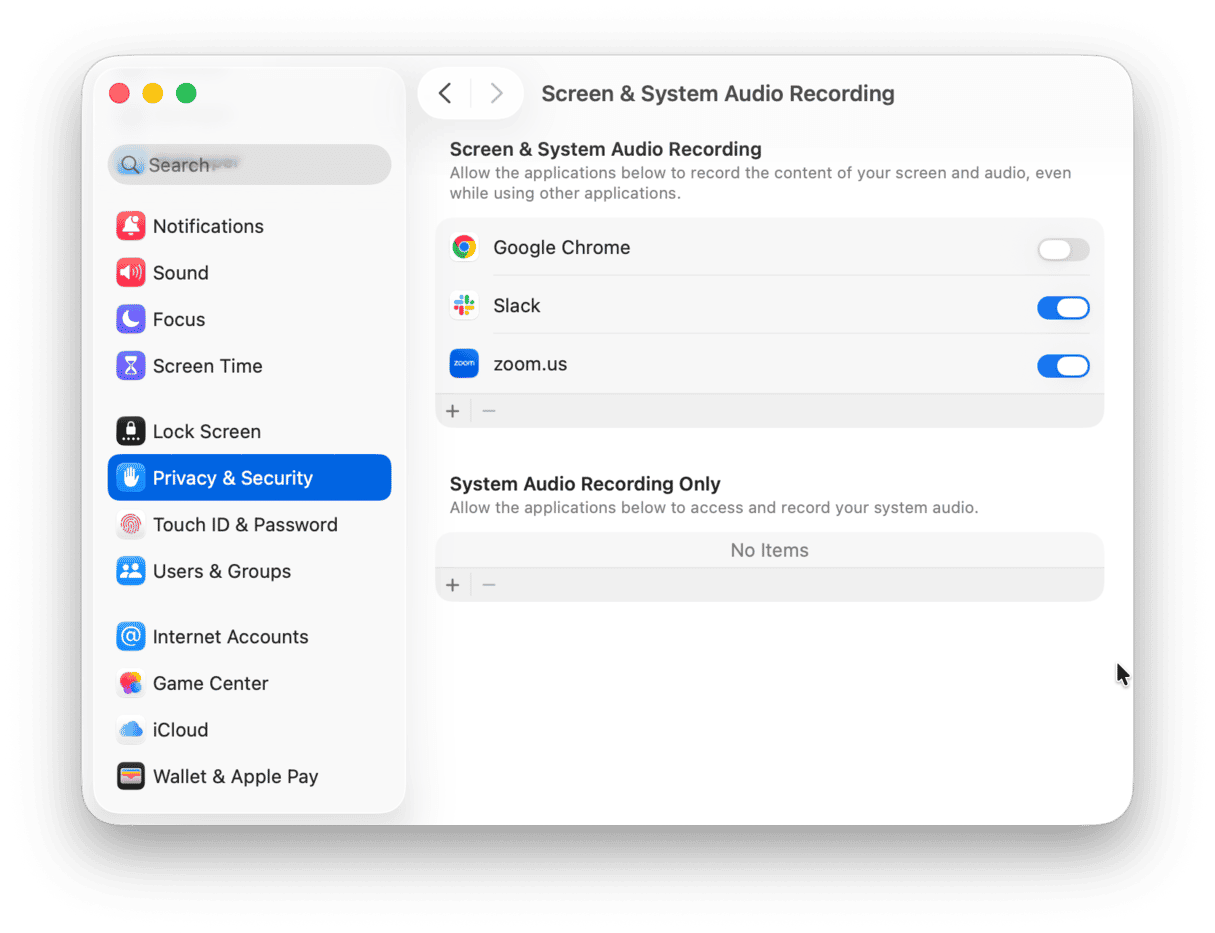
To enhance privacy and security even more, make your way through other tabs under Privacy and revoke unnecessary permissions.
Check for background launch agents
Some Mac apps, like Launch Agents, may not be visible on the surface. They will often initiate background checks or updates. So it's a good idea to check what's running in the background.
- Click Finder > Go > Go to Folder…
- Paste in this location:
~/Library/LaunchAgents
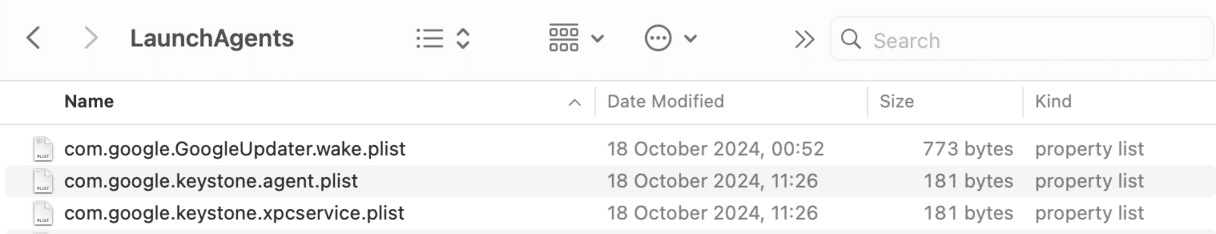
Look at the names of these apps. The part after .com indicates the name of the developer or the main app they belong to.
If you do not recognize some apps that appear there, the best thing to do is uninstall them. You can either do it manually by dragging them to Trash and hunting down leftover files or use a dedicated uninstaller tool to do the job for you. If you are not in the mood for manual app removal, we have a tip for you — CleanMyMac comes with the Applications tool that helps you get rid of apps once and forever within a few seconds.
- Start your free CleanMyMac trial (it's free for 7 days).
- After installing the app, open it and go to Applications from the sidebar.
- Click Manage My Applications and select the apps you’d like to uninstall.
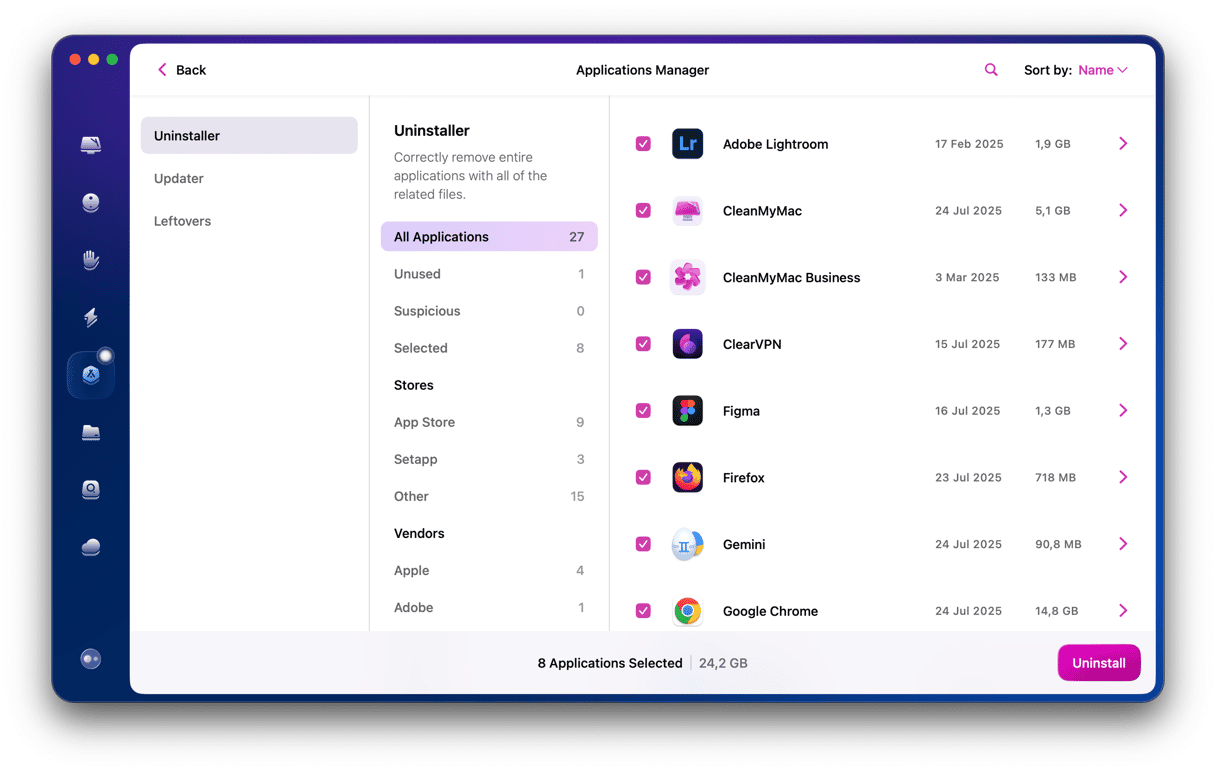
That’s it; app removal has never been easier.
Check login items
In addition to launch agents, it is also a good idea to check for other background processes — those that start up when you turn on your MacBook. You can do it from System Settings:
- Go to System Settings > General > Login Items & Extensions.
- Remove those you no longer need (select and click -). We recommend disabling all items except an antimalware app.
- Also, disable unnecessary app under App Background Activity.
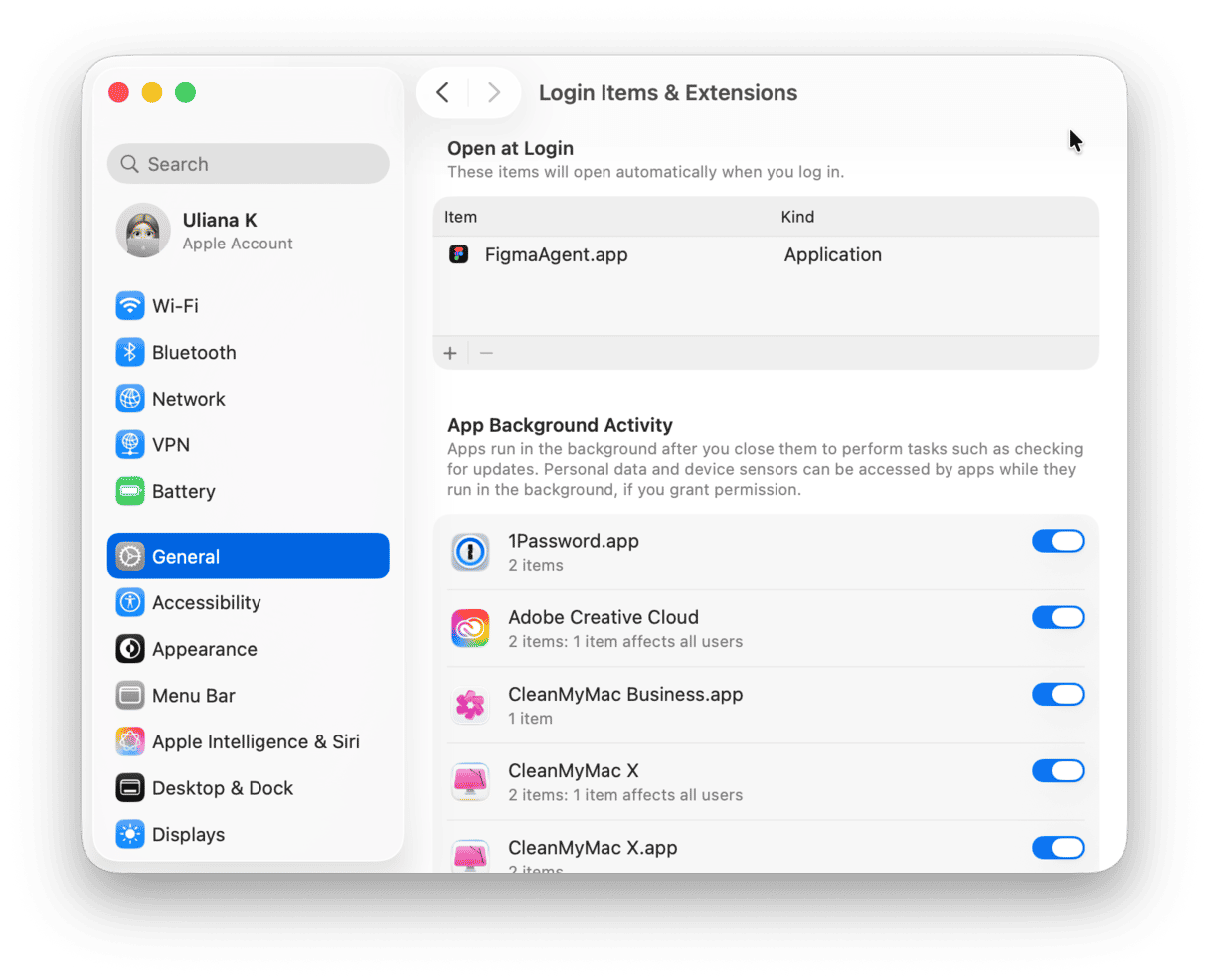
Pay specific attention to apps designed to work with graphics or screenshots like Wacom, Shottr, or DisplayLink. They require permissions to record your screen and may sometimes cause the notification. The same goes for Apple Remote Desktop or other VNC apps.
Turn off AirPlay and screen mirroring
Another potential reason behind the message that your screen is being observed is AirPlay or screen mirroring. What is interesting here is that it may be true that you’ve already finished using these features, but the message is still there. To check it, follow these steps:
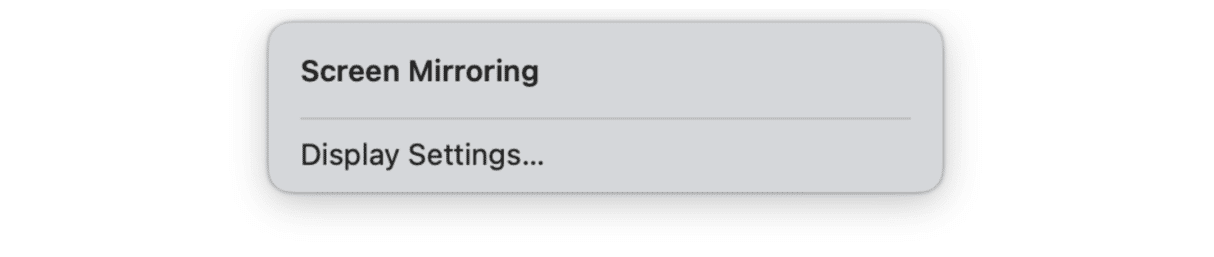
- From the menu bar, go to Control Center — it looks like an icon with switches.
- Click Screen Mirroring.
- No devices should be connected after you’ve stopped sharing.
Next, do the following:
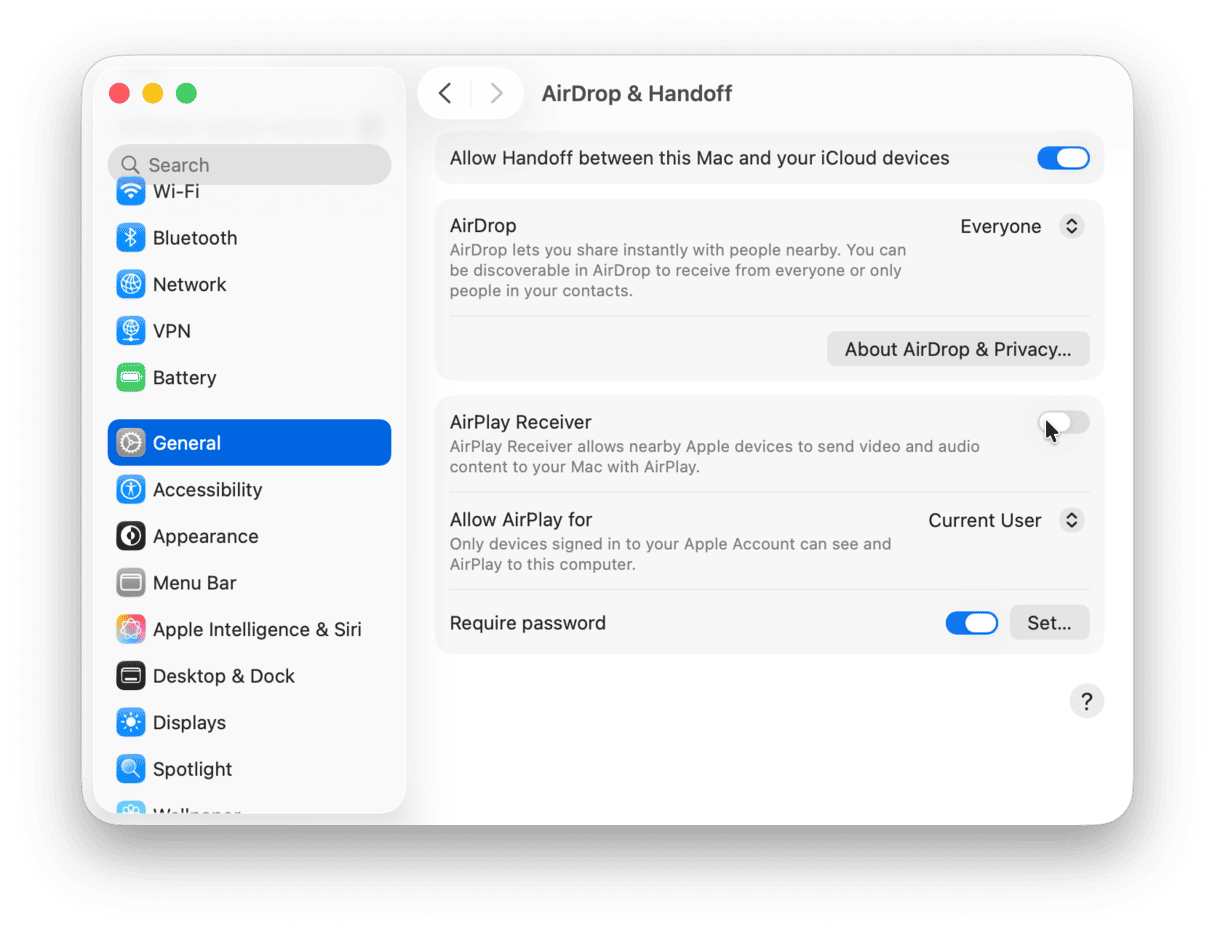
- Open System Settings from the main Apple menu.
- Go to General > AirDrop & Handoff.
- Turn off AirPlay Receiver if you do not plan to use AirPlay and type in your password to confirm the action.
If the message is still there, keep on reading.
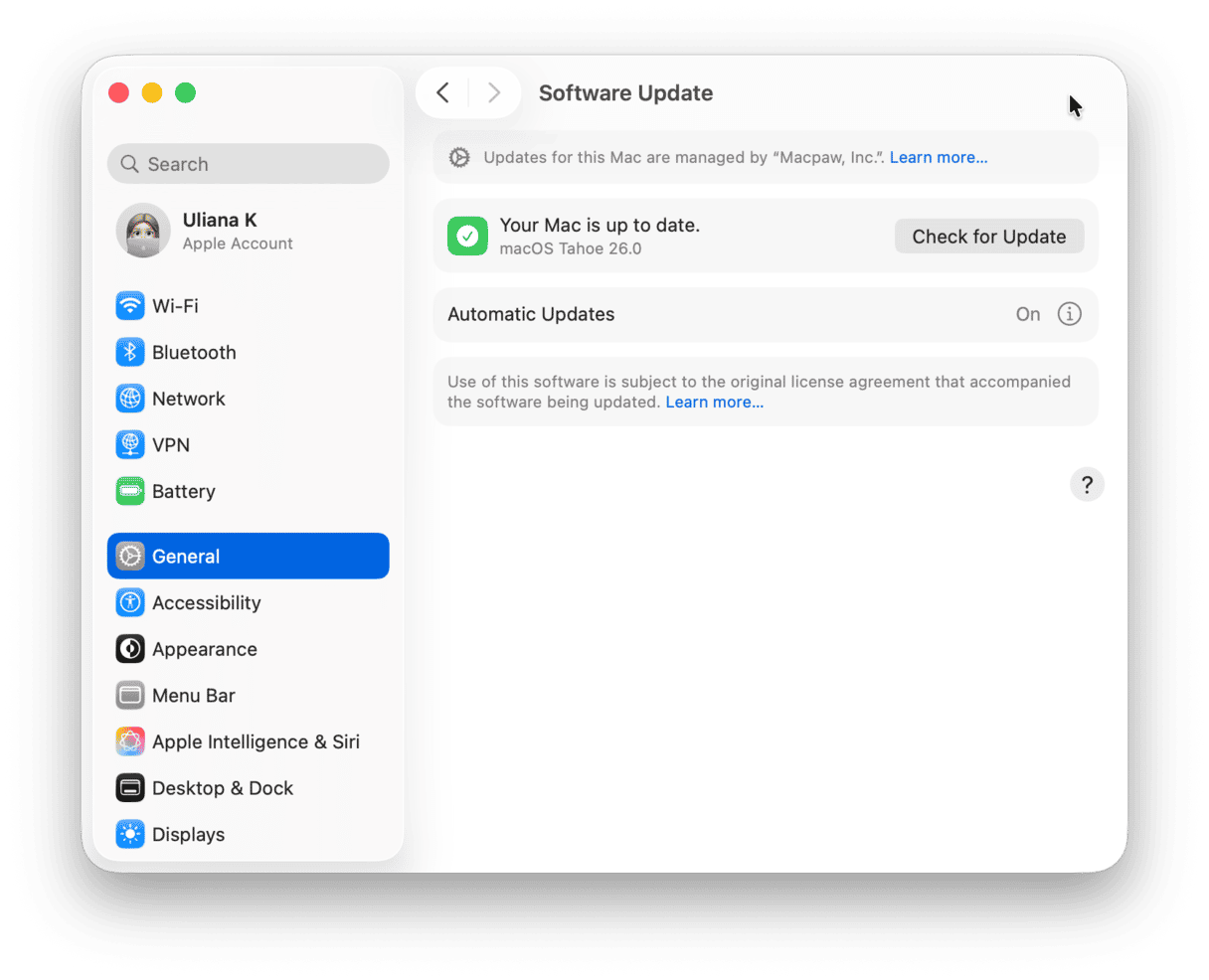
Update your Mac
It may be that the message appears because some important security updates are missing. Essentially, it means that your Mac is infected with a malicious app that built-in protection was unable to detect. Users on forums shared that the message even appeared on new Macs shipped with macOS Sequoia 15.4, and Apple later recognized that this specific macOS version had some security gaps that were addressed in macOS Sequoia 15.5.
In the next step, we’ll show you how to scan for malware. For now, take a few minutes to update your Mac:
- Go to System Settings > General > Software Update.
- Install any available updates.
Check for malware
If you’ve tried all of the tips above and nothing has helped, it is time to check your Mac for malware. If you see the “your screen is being observed” message or fear that your screen or Mac camera has been hacked, it may be spyware or ransomware.
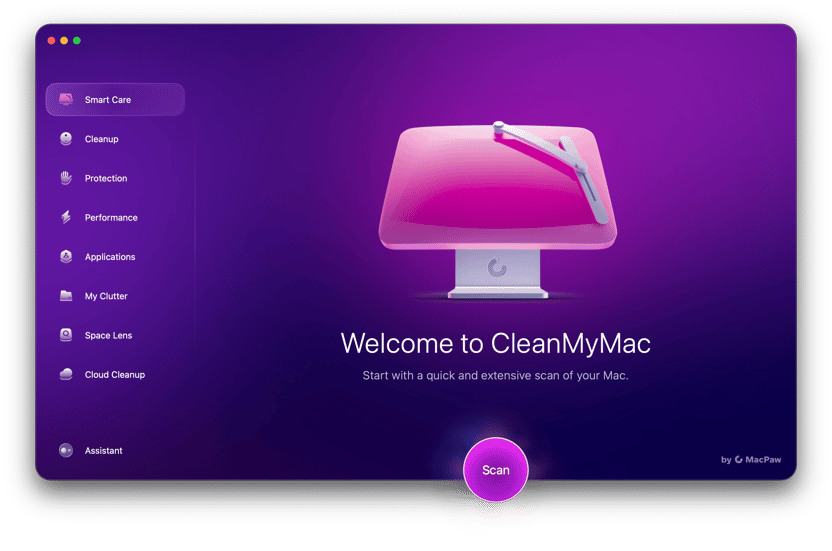
So, take the opportunity to scan your computer for malware. You can use the Protection feature in CleanMyMac. It uses a regularly updated malware database and compares what it finds on your Mac with it. Here’s how to run a Mac virus scan:
- Open CleanMyMac.
- Choose Protection from the sidebar and click Scan.
- Once the scan is complete, you will see if there are any types of threats to be removed.
- Click Remove, and CleanMyMac will remove any infection it has found.
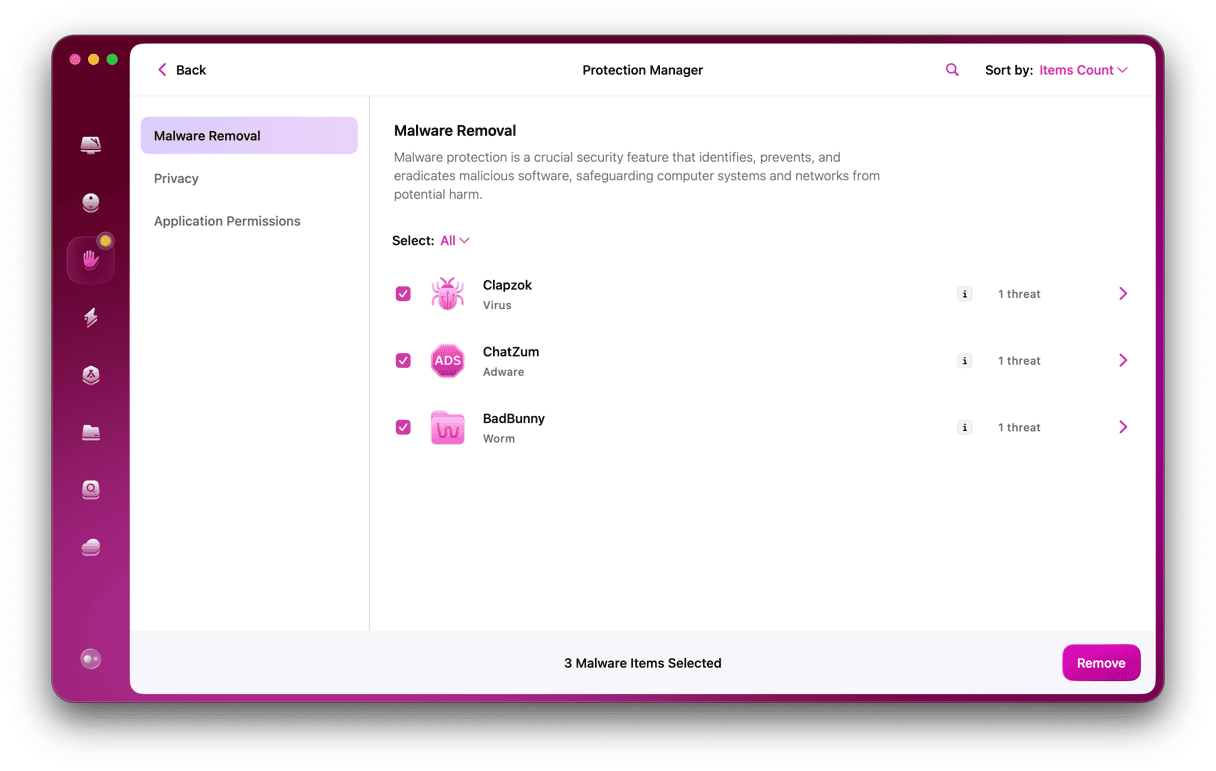
This app can detect macOS-specific keyloggers, backdoor viruses, and worms. Get your free CleanMyMac trial — you get access to all 25+ tools at zero cost. The app is notarized by Apple, meaning it’s safe.
Ensure you are not recording the screen
The ability to record the screen is among the most convenient and important features that come with macOS. To do it, you can use either the Screenshot utility or QuickTime Player. While most users know how to record screen on Mac, some of them may forget that it does not stop by itself. Instead, it should be stopped once it is no longer needed; otherwise, it will continue recording the screen even after you lock your Mac.
If it is the case, all you have to do is press Command-Control-Esc. It should stop screen recording instantly, and the alarming message should disappear right away. If this key combination has not worked, look for the icon shown below in the menu bar. Just click on it, and you’re done.

You should have fixed the issue by now; if not, head over to the final tip.
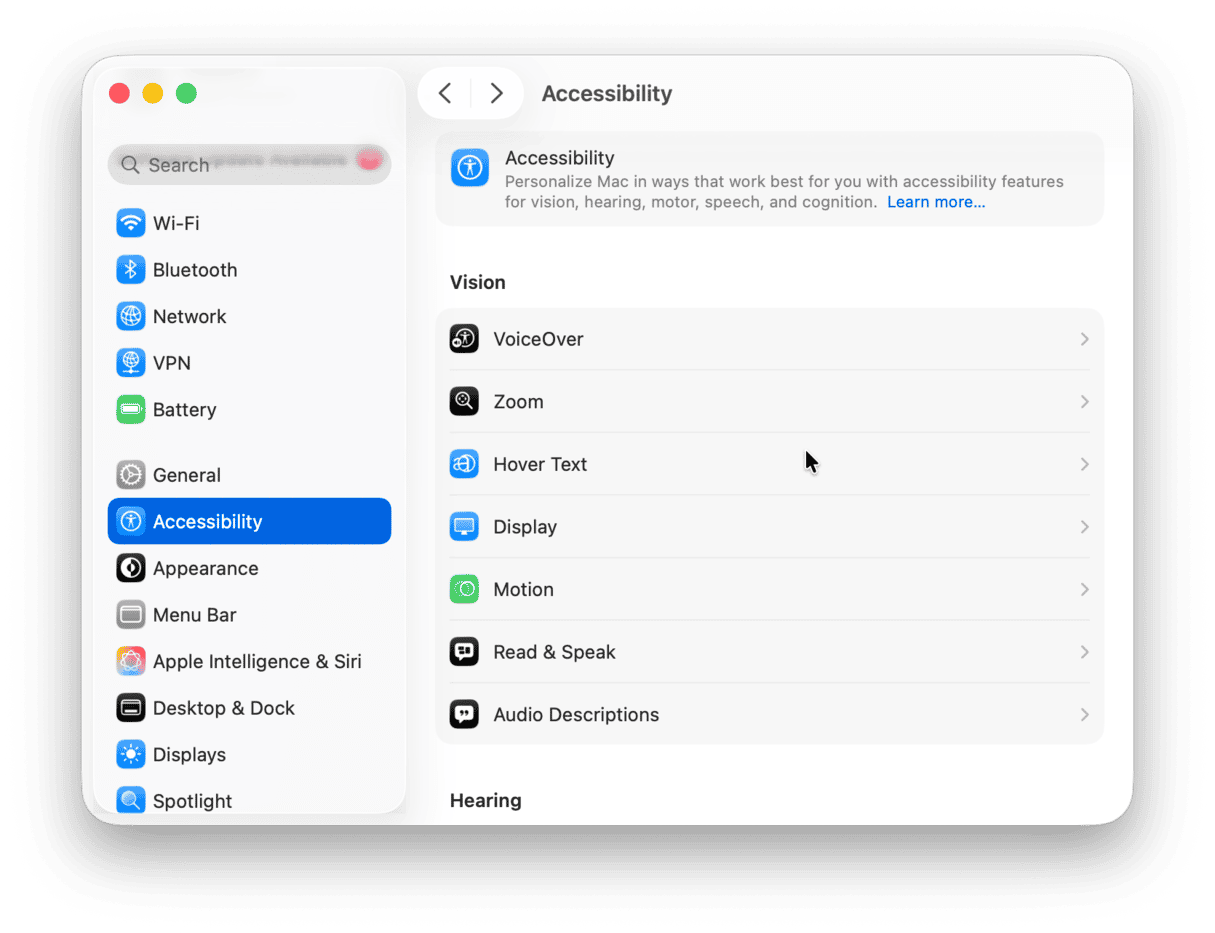
Check Accessibility features
Did you know that some Accessibility features may observe your screen, and so this notification will appear? Here are some of them:
- Zoom
- Switch Control
- Screen Curtain
- Accessibility Keyboard
- Invert Colors/Reduce Motion/Color Filters
To check if they are enabled, go to System Settings > Accessibility. If you do not need any of them, disable the features and check if the message disappears. Use search to find them easily.
Remove the message using Terminal
Finally, you can use Terminal to stop all screen sharing activity. The next step simply restarts the screen sharing agent on your Mac, which will close any remaining connections.
- Go to Applications.
- Type in: Terminal.
- In the Terminal App, paste this:
sudo killall screensharingd
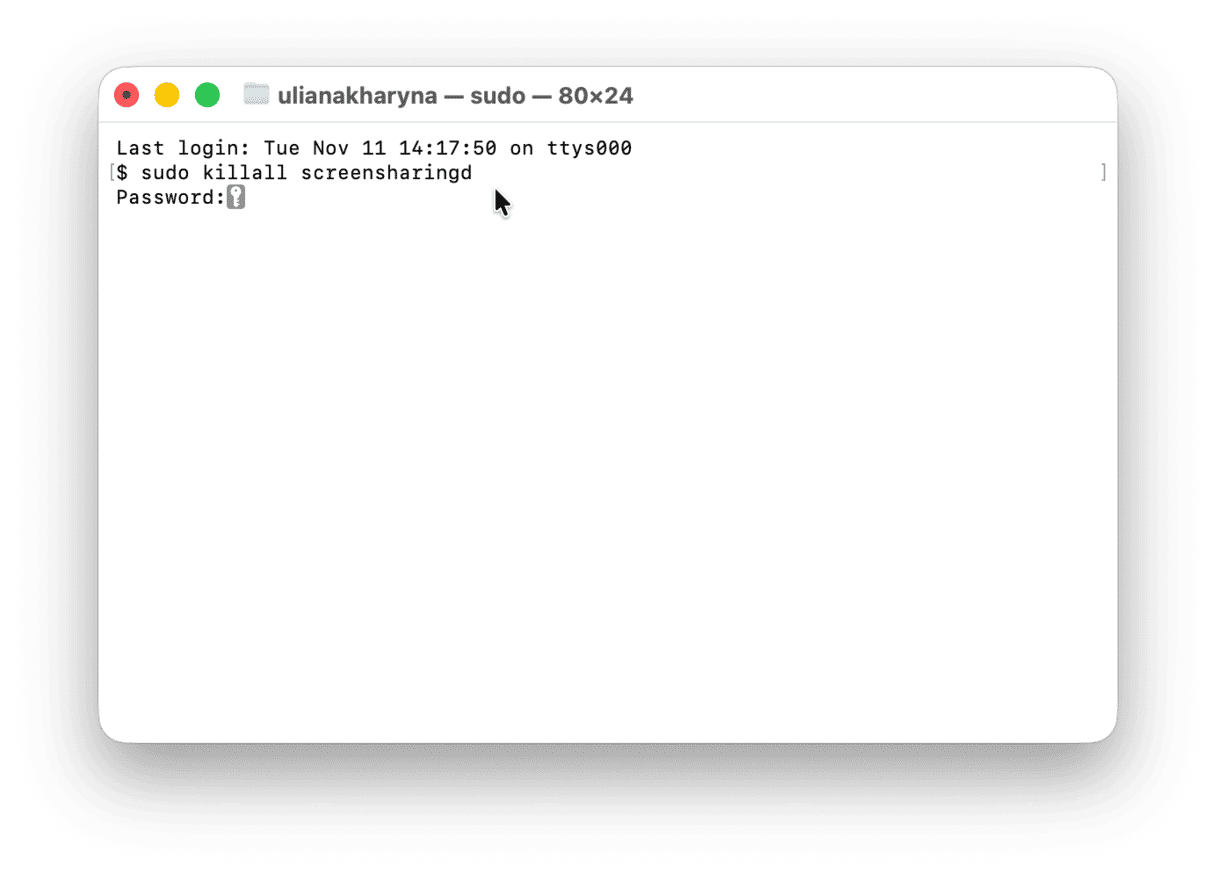
Next, enter your password. Press Return and you're done. The message "Your Mac is being observed" should disappear.
Seeing the “your screen is being observed” message on the lock screen can be alarming and scary. Most of the time, it appears as a result of your actions. In the most severe instances, it is due to having your Mac infected with malware. Either way, the issue is manageable, and hopefully, you could fix it by following one of the tips above.